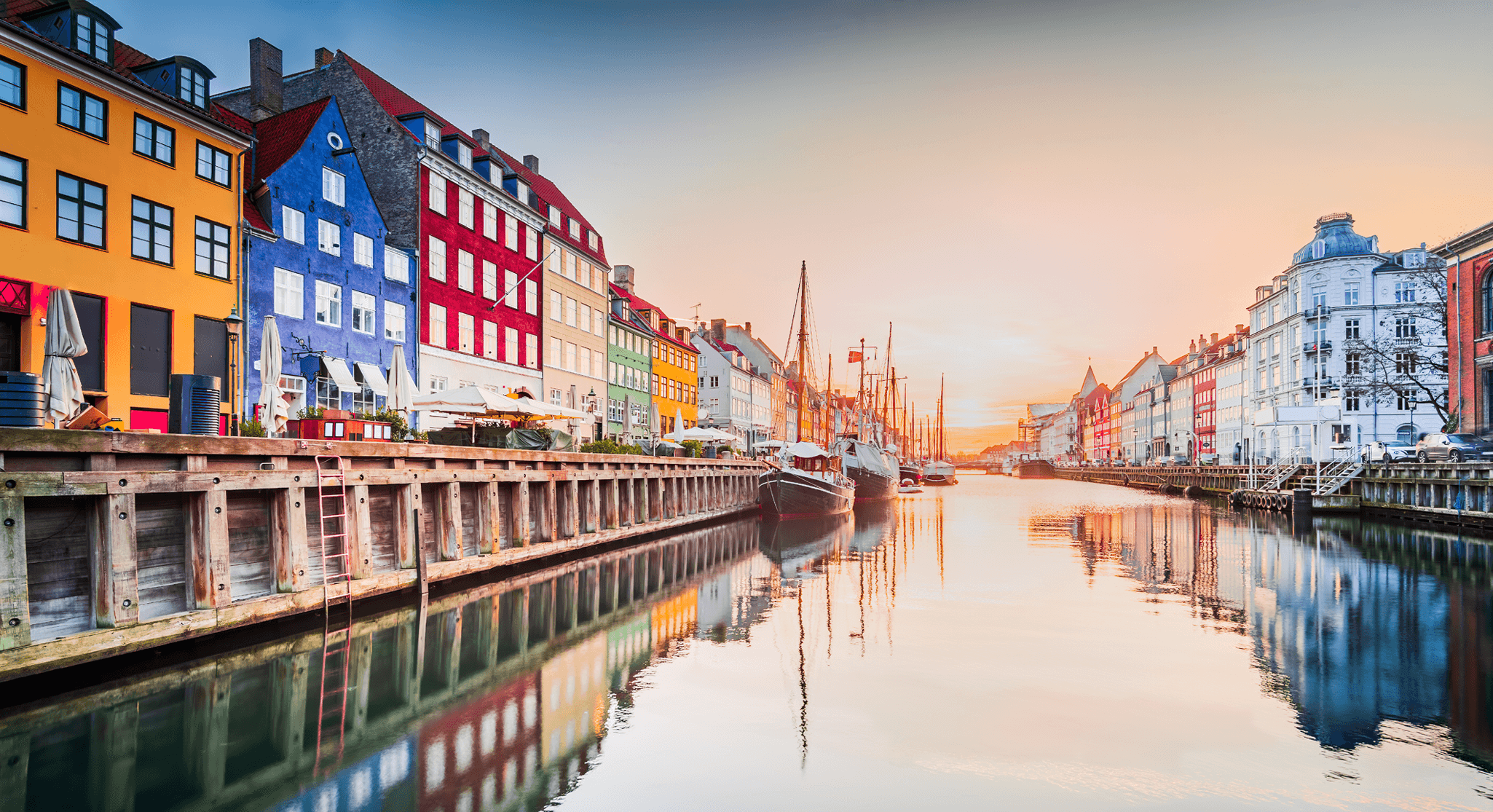
Asset tokenization: the next revolution in securities?
BlackRock, the world’s biggest asset manager, in March took a…
The benefits of deploying API solutions in FX trading
Foreign exchange traders have a wealth of technology options at…
Algo trading in India surges but still has room to grow
Algorithmic trading increasingly dominates stock markets, with around 80% of…
Regulating the Transformative Power of AI in Asset Management
Artificial intelligence (AI) is rapidly transforming our world, impacting everything…
Unlocking FX swaps: The migration to electronic channels gathers pace
NOTE: This article was originally published on e-Forex.net by Vivek…
Assessing the impact of electronification on sell-side markets
Markets have changed greatly over the past two decades, and…
The pressing case for workflow automation in fixed income
Workflow automation is not a new theme in the fixed…
How NBFIs can prepare for closer regulatory oversight
Non-bank financial intermediaries (NBFIs), colloquially referred to as “shadow banks”,…
UK Crypto Regulation: From Caution to Confidence
The UK’s approach to digital asset regulation has been characterized…
Implementing digital workflows: balancing innovation and compliance in capital markets
ION Group’s head of fixed income product development, Tommaso di…
Food for thought: ION Fidessa’s Regulation for Breakfast focused on the new FCA regulations
Recently, we welcomed colleagues from across the capital markets to…
Navigating the New Frontier – Regulating Crypto and Digital Assets
The explosive emergence of digital assets has reshaped the financial…
Retail brokers in Europe poised to expand derivatives as regulatory challenges mount
Changes are afoot in the derivatives industry as retail brokers…
SEC clearing mandate for US Treasury Securities
This article is written by a guest author. In the…
Capitalizing on the cloud in a fast-changing FX market
Foreign exchange is the largest financial market in the world,…
India’s ambitious move to same-day settlement and beyond
Confidence is high, and Indian authorities are in no rush…
The rise and future of credit portfolio trading
It’s a credit strategy that was off the radar several…
As connectivity gets more complex, new approaches are needed
The electronic trading landscape has undergone rapid transformation in recent…
Deciphering the meteoric rise of India’s capital markets
India is on the move and it’s moving fast. That’s…
Active Accounts at EU-based CCPs
Note: This article was originally published on the Clarus Blog…
Derivatives in 2024: Tech investment critical to competitiveness amid regulatory headwinds
Know your acronyms! This year promises to be full of…
What is the UK regulatory framework?
UK financial regulation is undergoing its most significant overhaul since…
2024: How technology is revolutionizing the securities finance industry
APIs, artificial intelligence, DLT, data harmonization, Cloud and smart contracts;…
Managing the nuances of securities finance in Asia
Securities finance in Asia is as diverse and complex as…
T+1 and FX: The opportunities and challenges of a shorter settlement cycle
28 May 2024 is set to be a pivotal moment…
Swaps Compression: What is it and why is it important?
This article is written by a guest author. Swaps Compression…
Repo: The heart of the global financial system and why the SEC took action
The US Securities and Exchange Commission (SEC) on 13 December…
Regulation matters: the near horizon for Europe in 2024
New EU transparency-related changes applied from 1 January 2024. To comply,…
Next generation FX analytics: Bringing transparency and more to the FX execution process
NOTE: This article was originally published on e-Forex.net by Vivek…
Achieving and maintaining an ultra-low latency FX trading infrastructure
NOTE: This article was originally published on e-Forex.net by Paul…
Migration to ISO 20022: the journey to more efficient cross-border trading
NOTE: This article was originally published on IBS Intelligence. Navigating…
FX trading risk management: Harnessing the benefits of Digital Transformation
NOTE: This article was originally published on e-Forex.net by Vivek…
Pathways to success: What steps are being taken to further optimise FX Post Trade Services?
NOTE: This article was originally published on e-Forex.net by Vivek…
How FX businesses can use data to boost customer loyalty and profitability
Digital transformation in the FX industry has changed how customers…
How an EMS helps firms navigate a fragmented fixed income market
Fragmentation in fixed income is nothing new. However, the situation…
FX market trends: Liquidity, execution, and the FX Global Code
In the ever-evolving world of foreign exchange (FX) trading, market…
The changing landscape of electronic trading in the APAC region
Electronic trading is on the rise in markets across the…
SEC Proposal to Mandate Climate Risk Disclosures
Sustainability is a contentious topic in the US, and the…
Upcoming changes in the Japanese equities markets
The Japan Exchange Group (JPX) has announced a range of…
Central Clearing of US Treasuries
U.S. Treasuries are one of the most liquid asset classes…
Consolidated Audit Trail: Preparing for the next phase of regulation
The Consolidated Audit Trail (CAT) has been a major focus…
Hong Kong’s new dual counter listings model: Challenges and opportunities for brokers
In June 2023, the HKEX launched its new dual counter…
Algorithmic trading – monitoring and management
The rationale for algorithmic trading has always been to reduce…
Is the reduction in Futures Commission Merchants (FCMs) about to reverse?
In the decade leading up to March 2020, the dual…
The new features of Fidessa Spotlight in two minutes
One of the initiatives we’re most excited about this year…
Preparing for upcoming UK regulatory changes
For more on the latest regulatory developments from the UK…
How large are Cleared Swap markets?
In today’s article I am going to look into the…
The road to desktop interoperability
Desktop interoperability is a longstanding concern for capital markets firms.…
Trading solutions for the Indian capital markets: The current landscape
The Indian capital markets are experiencing a period of rapid…
ION comes together to innovate at the annual technology competition in India
Developing and employing modern technology is at the heart of…
How can trading platforms support hybrid working?
The COVID-19 pandemic transformed millions of people into home workers…
The MiFID II Review – the Market Model Typology (MMT) post-trade data standard
For more on the MiFID II Review, see part one…
India introduces T+1 trade settlement
On 27 January 2023, the Securities and Exchange Board of…
The MiFID II Review is on the horizon
In Europe, the second Markets in Financial Instruments Directive and…
The India equities market in two minutes
The Indian capital markets are dynamic, diverse, and increasingly innovative.…
The rise of regional brokers in APAC presents challenges and opportunities
The ongoing process of economic development and integration in South-East…
The changing status of dark pools in the European equities landscape
Dark venues have been a significant part of the European…
The relationship of regulation with automation and technology
With advances in automated trading in recent years, regulators have…
XTP Spark: Back-office automation for trading businesses of any size
Life is complicated. Automation can make it simpler. At ION,…
Automation: What’s next and how will it alter the role of business leaders?
Note: This content was originally published by the FT Future…
Market volatility casts spotlight on realtime risk analytics
NOTE: This article was originally published on GlobalInvestorGroup.com by Radi…
Workflow automation through algo wheels – counting the costs?
The demands and expectations of buy-side firms are constantly driving…
The EU’s securities markets regulator prioritizes flagging of non-price forming trades
Following an earlier consultation, ESMA published its final report on…
The ION Desktop Interoperability Framework
ION introduces an open protocol, a desktop-side bus and a…
Software and industry evolution
Computer scientists have always tried to implement techniques to extend…
Catching up on events – 40 years of the ISIN
The 1980s brought us the first space shuttle, personal computers,…
Innovation at scale
Today, any global enterprise needs to innovate at speed. This…
FIX Connect technology of the future
The world of electronic trading has been changing rapidly over…
Elevate your FX business
The relevance of digital transformation Introduction The FX and cross-border…
Thoughts from the STA Market Structure conference 2021
We were among the many in-person participants at the Securities…
Trading algorithms of the future
As algorithmic trading has evolved over the years, both AI…
Differentiate, commoditize, and harmonize
Repo traders vying to make the most of the industry’s…
A cost-effective way to adopt Test Automation
Testing automation has become a fundamental step of the software…
Business Process Analysis – an ION perspective
A business process is a set of activities performed by…
Dark trading restrictions set to remain on the regulators’ watch lists
The UK Treasury’s Wholesale Markets Review consultation paper devotes some attention to…
How do you manage non-functional requirements?
If you are in the software industry, you’re already familiar…
Automation of existing software platforms: Part 3
Customization of existing trading platforms is a vital process within…
MiFID II review stores up more compliance costs
As part of the ongoing wider review of MiFID II,…
Optimizing FX STP through intelligent automation
Today’s digital and data-driven economy has placed an ever-increasing range…
UK regulators hit the reset button
As the UK gets ready to hit the reset button…
Real-Time Database Technology you can bank on
Advances in Real-time Database technology are driving faster order throughput…
Display Order Facility in US Equity Markets
Efficient price discovery is essential to the smooth functioning of…
Scalable data caching requires scalable querying – here’s how to achieve it
Modern fintech applications have to process enormous volumes of data.…
Automation of existing software platforms – part 2
Evolving the capability of existing trading platforms is a vital…
GTP Stitching
Effective and accurate order management is fundamental to robust trading.…
Successful consolidated audit trail Phase 2c go live
On April 26, ION Markets marked a significant Consolidated Audit…
The structured, the nimble, and the delegator.
A tale of data from the BrokerTec migration to CME.…
Similarities between Apple’s new M1 chip and a trading system design?
I started my new Apple Mac with its new M1…
Low-Touch woes vs Restaurant Wars
The other night, I was rewatching an episode from the…
The easy way to make your trading apps work together as one
Trading is a complex business. In fast-moving, competitive markets, traders…
Back to Front in Cleared Derivatives
Imagine a world where the connections between the front office,…
Regulatory challenges of trading Asian equities and the growth of the Swaps market
When trading equities around the world, most investors understand the…
Should a software house still invest in technology?
I was reading an article on how LinkedIn uses Kafka…
Automating existing software platforms
Adding additional automation within existing order workflow systems is never…
Back to school for MiFID II
The review of MiFID/MiFIR is now well underway following the…
Driving customer excellence
How a business develops its products and delivers its services…
AI: Paving the way towards perfect STP rates
The last decade has seen a remarkable rise in applied…
For those obsessed with quality
Have you said “wow, this is exactly what I wanted”…
All algos are not equal
Algorithms have made their way into our daily lives, from…
Asset management in the cloud: A choice or a transition?
As on-premises solutions have gradually given way to hosted services,…
Correlations hurt your decision-making (not just your portfolio)
Decision-making in contexts that aren’t always easy to predict —such…
Doing a UX re-design for your product
“It is not the strongest of the species that survives,…
The road to SaaS and other myths
Some estimates say that in a few years SaaS will…
The future of trading system display technology
Following my recent article on trading screen design, I had…
Brexit: Liquidity shifts post transition period
After a difficult 12 months, Brexit finally happened. However, the…
Is traditional D2C repo dying?
As D2C repo goes electronic, having the right systems in…
Finding investment opportunities while remaining compliant in a volatile new world
When I meet regulatory and investment compliance officers in the…
Brexit: Cross-border trade publication
Under MiFID post-trade transparency rules, equity trades must be published…
How FX businesses can boost customer loyalty and profitability by using data intelligently
Digital transformation in the FX industry has changed how customers…
Partial settlement: The CSDR effect
Does your secured funding business support partial settlement? Or rather,…
A state of FLUX: How findings led UX helps us create the solutions our users really need
If you had 1 hour to solve a problem, what…
A new asset class comes to town!
We often hear in the press of new trading venues,…
Voice trading after MiFID and COVID: It’s time to stop worrying and embrace digital transformation
Voice trading has undergone major changes as a result of…
There’s no cloud, it’s just somebody else’s PC
Cloud-based applications are great. They free users from hardware, obsolescence,…
The future of web development
The web ecosystem is evolving at an insane speed. Driven…
Here’s why you need to automate your business analytics
Information is different than knowledge. And the more information you…
The benefits of a good order management system during a pandemic
Trading rooms of the world have been shrinking since the…
Brexit: MiFID Share trading obligation – Should the EU investors be worried?
The European Union’s MiFID directives set clear rules on the…
Let’s talk latency
Trading is a highly competitive business where speed is of…
Three display functions that all trading systems should embrace
When trading moved from trading floors and into the digital…
Spanish tax set for January 2021
Before the advent of an EU financial transactions tax (FTT),…
Recurring waves of Brexit
In the face of recurring Brexit waves, the markets have…
Working towards a common goal
Regulators globally are continuing to step up efforts to monitor…
Wider adoption of MMT encouraged
The Securities and Markets Stakeholder Group (SMSG) recently advised ESMA to…
The evolving global impact of MiFID II
Last week, the U.S. Securities and Exchange Commission announced an…
Catch 22: The share trading obligation
MiFID II refined the definition of OTC trading for equities,…
Time runs out on Swiss equivalence
Over the weekend, the stock market equivalence granted to Switzerland…
Load More